Security tips for the tech-phobe

…Because someone, somewhere has access to everything you ever do online.
Words:Alon Aviram
Illustration: Luke Carter
Until recently, I dismissed the idea of using encrypted emails or other digital security measures as unnecessary, delusional and even a tad-bit egotistical. After all, if you’ve got nothing to hide, you’ve nothing to fear, right?
Stereotypes came to mind of those who toyed with these dark arts; from computer nerd, spook, and cyber criminal, to tinfoil hat-wearing conspiracy theorist. Like many, I nurtured a slight phobia for anything digital that wasn’t instantly easy to use, or didn’t look good; something Google is all too slick at providing.
Now, in the post-Snowden age, there’s growing public awareness that nothing is private, from your Skype video call with your nan, to Facebook chats with mates. Yet despite this most of us do little to protect ourselves. We close the door to our house, but leave the gate to our digital lives wide open.
Mass surveillance and data collection is often justified as an unfortunate but necessary measure to protect us; a feature of our modern lives which shouldn’t concern your average upstanding citizen.
But think of the challenge put forward by journalist Glenn Greenwald, who asks conference attendees to give him all their emails and passwords: “Not just the nice, respectable work one in your name. But all of them, because I want to be able to just troll through what it is you’re doing online, read what I want to read and publish whatever I find interesting. After all, if you’re not a bad person, if you’re doing nothing wrong, you should have nothing to hide. Not a single person has taken me up on that offer.”
Any serious crook or spiv is already familiar with digital security measures. It’s the people who don’t think they have anything to hide who may have plenty to fear. So here are some tips and applications, which even the tech-phobic greenhorn can use. These basic measures will definitely not provide you with total digital security. But they may deter the opportunist, and make the work of determined attackers a little more costly.
- Passwords: Don’t use your mum or dad’s name. Learn how to set a strong password here in order to improve your personal security. Then use this password checker to see how strong it is.
- Signal: An encrypted communications mobile phone app. Kind of like whatsapp, but open-source, meaning that experts can inspect the application to ensure there aren’t any vulnerabilities. Signal (Apple/android ) won’t disguise your mobile phone’s location (and therefore won’t protect you from IMSI-catcher tracking), but all your messaging and phone calls via the app are encrypted so no one can read them.
- Tor Browser: Like say Firefox or Safari, Tor is an internet browser. It disguises your identity so you can browse the web anonymously. You can download it on your phone and desktop.
- Encrypted email: Slightly difficult to set up, but fairly plain sailing to work. Using encrypted emails scrambles the content of your emails into (as of yet) an unbreakable code, preventing government agencies and hackers from reading them. Read the Centre for Investigative Journalism’s how-to-guide for installation and use.
- Tails: You can start Tails on almost any computer using a DVD, USB stick, or SD card. Tails is a live operating system, that you can start on almost any computer from a DVD, USB stick, or SD card. It aims at preserving your privacy and anonymity, and doesn’t leave a trace of your activity on the computer once you’ve exited.
- Don’t connect to your personal online accounts on devices — computers, laptops, tablets, smartphones — that aren’t yours. Typing your password into a public workstation at a hotel, an internet cafe, or even a friend’s house means that anyone who has taken control of that machine now knows your passwords.
- Sign out of your email or social media accounts while you surf. Signing in to a browser or web service, such as Gmail or Facebook, while you surf allows that service to easily track what you do and where you go online. Sign in only when you specifically need to do so.
- Install software updates. One of the most common ways hackers attempt break-ins is by exploiting known flaws or bugs in the various applications that are installed on a computer. When responsible application designers learn about such vulnerabilities, they issue a patch to fix the matter. That’s why it’s important to keep all of the software on your devices as up-to-date as possible.
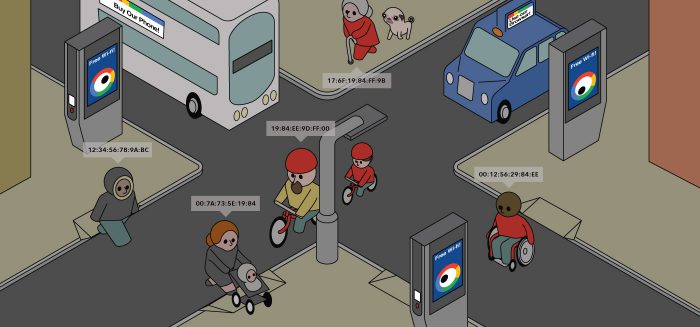
A Cable investigation recently exposed one element of a much wider world of surveillance and gave us a bit of a jolt. Our findings revealed that Avon & Somerset police and at least six other police forces nationally had purchased IMSI-catchers. These indiscriminate surveillance devices steal data from hundreds of mobiles a minute within an eight square kilometre area. The technology tracks the movement of phones in real-time, with the capacity to read text messages and listen to the phone calls of thousands of people.The response by Avon & Somerset police and other named forces was to take the public documents cited in the investigation offline, and to neither confirm or deny that they possess or use the technology. This response is worrying and does little to garner public trust in policing.
As it stands the public are left in the dark, unaware of which legislation and police guidelines govern the use of these mass surveillance devices. Until British security and police services come clean on the use of IMSI-catchers and the countless other data surveillance tools, we do have something to fear: the unknown.
In 2015, Vice News and Privacy International recorded tell-tale signs of IMSI-catcher use at anti-austerity demonstrations in London, raising fears that protesters were being secretly monitored. Following the Cable investigation, the Bristol branch of the National Union of Journalists demanded that Police and Crime Commissioner, Sue Mountstevens, answer how journalists and their sources are protected from IMSI-catcher snooping. They still await a proper response. Police aside, IMSI-catchers are available on the open market, meaning that private actors are likely using the technology in the UK. There have even been reports in the US of industrial espionage, with companies finding IMSI-catchers strapped onto lampposts outside offices.
Do you have any top tips? Please comment below get in touch and I will be happy to add suggestions.
With thanks to Mat Alborough and the ACLU report for their information security recommendations.








Report a comment. Comments are moderated according to our Comment Policy.
This sort of technology is needed more then ever with
http://www.wired.co.uk/article/ip-bill-law-details-passed